/home $ GODEBUG=gctrace=1 k6 run --system-tags proto,subproto,status,method,url,group,check,error,error_code,tls_version,scenario --out influxdb=http://influxdb:8086/k6_db ./main_yaam.js
/\ |‾‾| /‾‾/ /‾/
/\ / \ | |_/ / / /
/ \/ \ | | / ‾‾\
/ \ | |‾\ \ | (_) |
/ __________ \ |__| \__\ \___/ .io
execution: local
script: ./main_yaam.js
output: influxdb=http://influxdb:8086/k6_db (http://influxdb:8086)
scenarios: (100.00%) 2 executors, 450 max VUs, 30m30s max duration (incl. graceful stop):
* UC_revoke: Up to 0.00 iterations/s for 30m0s over 1 stages (maxVUs: 10-50, exec: UC_revoke, gracefulStop: 30s)
* UC_use_RP: Up to 150.00 iterations/s for 30m0s over 2 stages (maxVUs: 400, exec: UC_use_RP, gracefulStop: 30s)
UC_revoke ✗ [--------------------------------------] 10/10 VUs 00m00.0s/30m0s 0 iters/s
UC_use_RP ✗ [====>---------------------------------] 400/400 VUs 04m13.8s/30m0s 043 iters/s
gc 1 @0.008s 2%: 0.007+0.45+0.20 ms clock, 0.063+0.11/0.30/0.48+1.6 ms cpu, 4->4->1 MB, 5 MB goal, 8 P
gc 2 @0.010s 4%: 0.005+0.54+0.19 ms clock, 0.040+0.12/0.22/0.47+1.5 ms cpu, 4->4->2 MB, 5 MB goal, 8 P
gc 3 @0.018s 3%: 0.012+1.6+0.022 ms clock, 0.096+0/0.67/0.96+0.17 ms cpu, 6->6->4 MB, 7 MB goal, 8 P
gc 4 @0.051s 2%: 0.007+4.3+0.025 ms clock, 0.058+0.19/6.4/2.6+0.20 ms cpu, 8->8->8 MB, 9 MB goal, 8 P
gc 5 @0.106s 3%: 0.007+21+0.026 ms clock, 0.063+1.1/24/10+0.21 ms cpu, 15->17->15 MB, 16 MB goal, 8 P
gc 6 @0.165s 2%: 0.010+55+0.067 ms clock, 0.080+0.25/10/22+0.54 ms cpu, 29->31->20 MB, 30 MB goal, 8 P
gc 7 @0.273s 2%: 0.016+6.9+0.023 ms clock, 0.12+0.31/7.5/21+0.18 ms cpu, 39->40->18 MB, 41 MB goal, 8 P
gc 8 @0.366s 2%: 0.010+5.1+0.023 ms clock, 0.086+0.084/8.9/18+0.18 ms cpu, 36->36->20 MB, 37 MB goal, 8 P
gc 9 @0.507s 2%: 0.011+18+0.028 ms clock, 0.094+0/32/21+0.22 ms cpu, 40->40->22 MB, 41 MB goal, 8 P
gc 10 @0.722s 1%: 0.010+6.8+0.025 ms clock, 0.081+0.21/8.6/18+0.20 ms cpu, 43->43->19 MB, 44 MB goal, 8 P
gc 11 @0.894s 2%: 0.008+28+0.028 ms clock, 0.065+0.13/55/135+0.22 ms cpu, 38->39->26 MB, 39 MB goal, 8 P
gc 12 @1.115s 2%: 0.009+12+0.038 ms clock, 0.073+0.19/23/53+0.30 ms cpu, 50->51->28 MB, 52 MB goal, 8 P
gc 13 @1.381s 2%: 0.009+40+0.026 ms clock, 0.073+0.18/79/183+0.21 ms cpu, 56->56->29 MB, 57 MB goal, 8 P
gc 14 @1.697s 2%: 0.008+26+0.007 ms clock, 0.068+0.25/51/129+0.061 ms cpu, 57->57->29 MB, 58 MB goal, 8 P
gc 15 @1.932s 2%: 0.007+5.8+0.028 ms clock, 0.062+2.6/11/22+0.23 ms cpu, 58->59->22 MB, 59 MB goal, 8 P
gc 16 @2.023s 3%: 0.63+97+0.006 ms clock, 5.0+98/192/0+0.049 ms cpu, 44->47->32 MB, 45 MB goal, 8 P
gc 17 @2.224s 5%: 0.94+195+0.028 ms clock, 7.5+290/213/0+0.23 ms cpu, 62->69->49 MB, 65 MB goal, 8 P
gc 18 @2.629s 7%: 0.088+391+0.053 ms clock, 0.71+116/606/0+0.42 ms cpu, 88->103->76 MB, 99 MB goal, 8 P
gc 19 @3.236s 12%: 83+509+0.029 ms clock, 670+474/930/0+0.23 ms cpu, 134->160->118 MB, 153 MB goal, 8 P
gc 20 @4.335s 14%: 0.19+987+0.031 ms clock, 1.5+456/1886/0+0.25 ms cpu, 197->246->184 MB, 236 MB goal, 8 P
gc 21 @6.029s 15%: 0.77+1498+0.037 ms clock, 6.1+191/2994/0+0.30 ms cpu, 300->382->288 MB, 369 MB goal, 8 P
gc 22 @8.731s 17%: 3.8+2486+0.043 ms clock, 30+817/4971/0+0.34 ms cpu, 466->593->444 MB, 577 MB goal, 8 P
gc 23 @12.822s 17%: 0.11+3998+0.043 ms clock, 0.91+495/7907/0.048+0.34 ms cpu, 711->913->688 MB, 889 MB goal, 8 P
gc 24 @19.625s 16%: 2.2+3796+0.005 ms clock, 17+99/7591/4841+0.046 ms cpu, 1101->1265->916 MB, 1376 MB goal, 8 P
GC forced
gc 25 @143.424s 2%: 0.10+1599+0.067 ms clock, 0.82+1.5/3104/9075+0.54 ms cpu, 1110->1116->828 MB, 1833 MB goal, 8 P
GC forced
gc 26 @265.035s 1%: 0.11+1590+0.005 ms clock, 0.88+0.84/3181/8818+0.042 ms cpu, 1370->1376->830 MB, 1657 MB goal, 8 P
^C
running (04m14.2s), 000/410 VUs, 5491 complete and 86 interrupted iterations
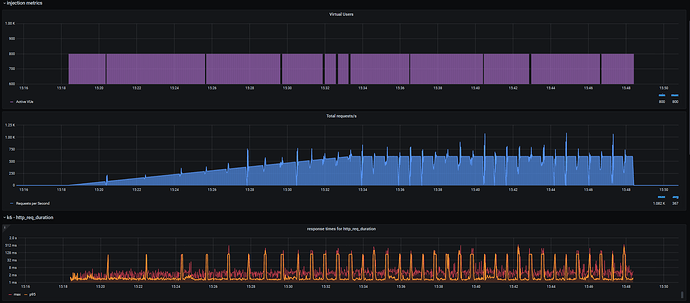
Oscillations occur exactly on GC #25, #26, and so on…